PDF) Security of Telemedical Applications over the Internet using Programmable Cellular Automata | Petre Anghelescu - Academia.edu
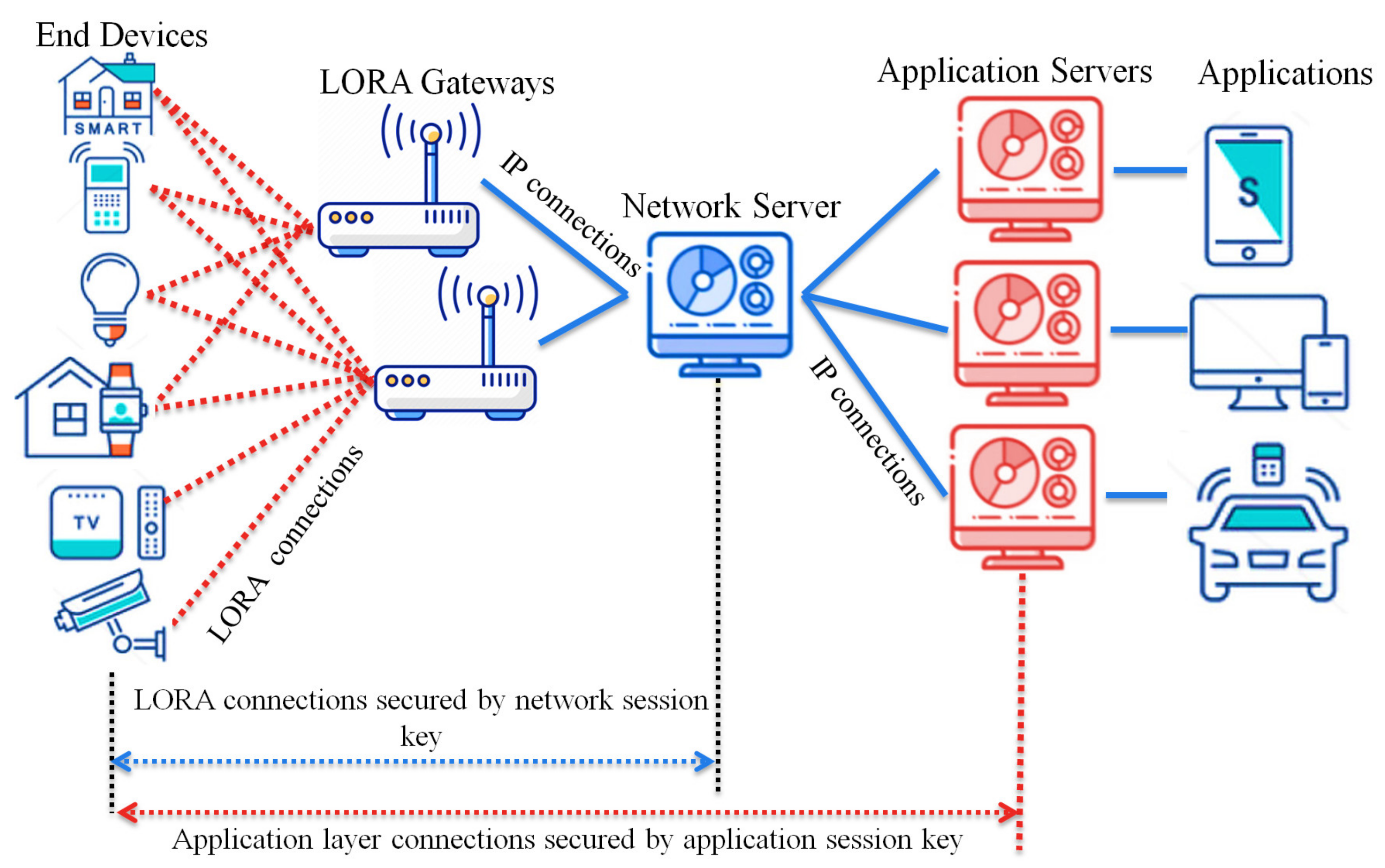
Sensors | Free Full-Text | A Key Management Protocol Based on the Hash Chain Key Generation for Securing LoRaWAN Networks
Language and Automata Theory and Applications: 10th International Conference, LATA 2016, Prague, Czech Republic, March 14-18, 2016, Proceedings | SpringerLink
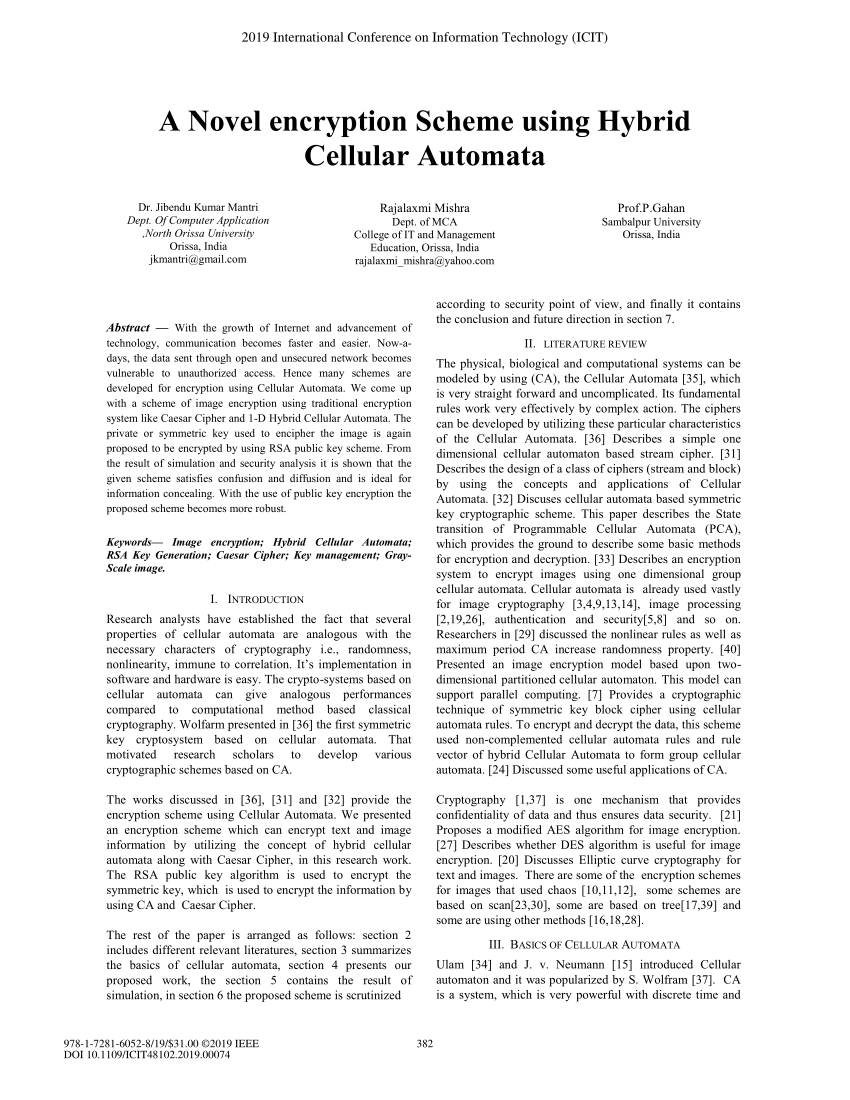
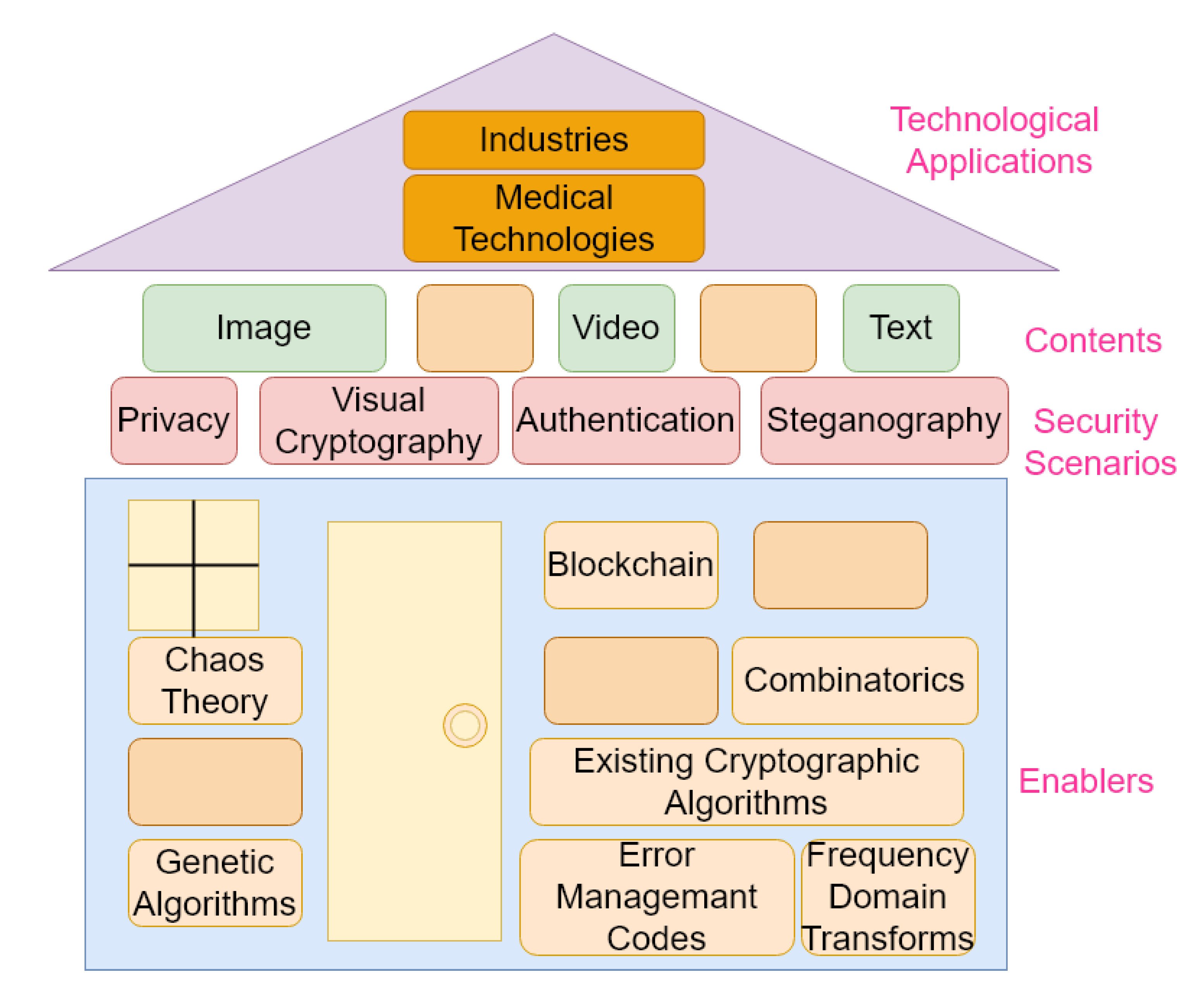
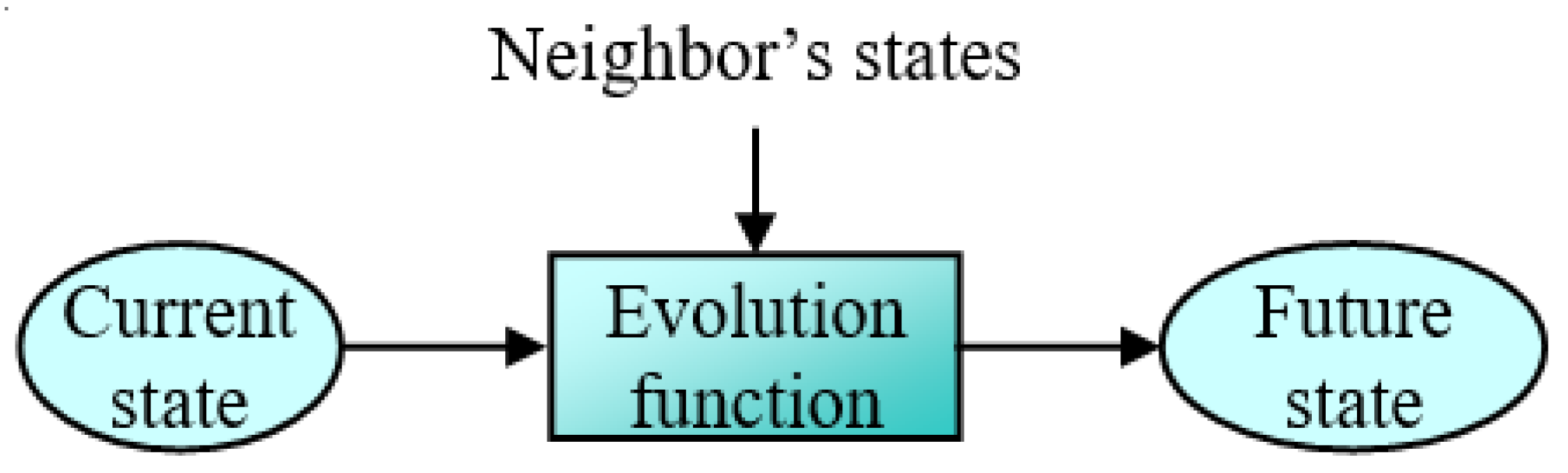
![PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/19fc3d51392b69ea11e436a91eda596b6c613c53/4-Figure2-1.png)
PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar
![PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/19fc3d51392b69ea11e436a91eda596b6c613c53/1-Figure1-1.png)
PDF] A Lightweight Cellular Automata Based Encryption Technique for IoT Applications | Semantic Scholar

Automata-2008: Theory and Applications of Cellular Automata: Adamatzky, A., Alonso-Sanz, R., Lawniczak, A.: 9781905986163: Amazon.com: Books

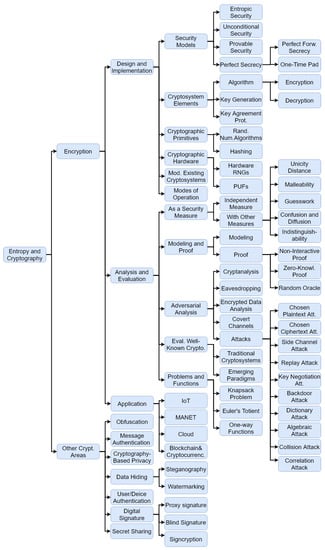
![PDF] On the Applications of Cellular Automata and Artificial Life | Semantic Scholar PDF] On the Applications of Cellular Automata and Artificial Life | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/59885b8e0600b82a8274788ba067b6494dfe3f1b/1-Figure1-1.png)